This course addresses one of the most commonly overlooked areas of the pen testing process, evasion and countermeasure bypass. This course shows you how to remain undetected and penetrate deeper into systems and networks for maximum effectiveness. In this course, Exploitation: Evading Detection and Bypassing Countermeasures, you’ll learn how to go undetected and penetrate deeper into systems and networks for maximum effectiveness. First, you’ll learn how to remain anonymous during all phases of the kill chain. Next, you’ll discover how to bypass network and application firewalls. Then, you’ll learn how to sneak past intrusion detection systems and honeypots. Finally, you’ll learn circumventing application security controls and how to fool anti-virus software. By the end of this course, you’ll have learned how to use numerous hands-on tools and techniques to craft surgical exploits that will allow you to penetrate deeper into sanctioned networks and remain completely undetected throughout the process.
| Course Price | Original price was: $50.00.$3.00Current price is: $3.00. |
Course Description
What you’ll learn
- 100+ videos (20+ hours) to teach you Evading Security Controls from scratch.
- Use 20+ hacking tools
- 85+ hands-on real-life hacking examples.
- Evading Detection and Bypassing Countermeasures
- Remaining Anonymous
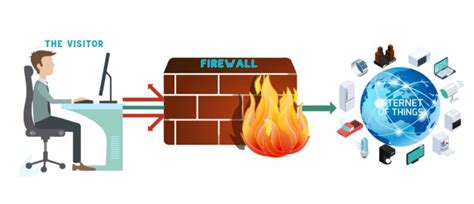
- Bypassing Network Firewalls
- Sneaking Past Intrusion Detection Systems and Honeypots
- Circumventing Application Security Controls
- Fooling Platform Controls
- Outwitting Platform Memory Controls
- Mapping Evasion Techniques to Kill Chains
This course includes:
- 20+ hours of hacking content
- FREE Hacking tools, resources used in this course and latest hacking books available for Bypass Security Controls.
- 24/7 availability for support, so if you have any questions you can email or chat with us and we’ll respond to you within 15 hours.
NOTES
- This course is created for educational purposes only and all the attacks are launched in my own lab or against systems that I have permission to test.
- This course is totally a product of Cyber Hacking, no other organization is associated with it or a certification exam.
Who this course is for:
- Anybody interested in learning Evading Security Controls, penetration testing and ethical hacking
- Security specialists
- Beginners White Hat Hackers and Pentesters looking to learn practical password cracking
- Information Security Professionals who want to enhance their practical skill set
- Digital and Computer Forensics Experts looking to excel in information and evidence gathering
- Anybody interested in learning ethical hacking / penetration testing




Reviews
There are no reviews yet.